Madhup
Kumar Yadav
I build high-performance, user-focused digital products and websites for small businesses. From idea to deployment, I ship with quality and speed.
ABOUT
THE BUILDER
Building Digital Products

Madhup Kumar Yadav
Full Stack Developer
Pursuing B.Tech in IT at Amity University, Noida. I operate at the intersection of product thinking and engineering execution to ship reliable, high-performing software.
Full Stack Delivery
Building user-focused web products from concept to launch with robust frontend architecture and reliable backend systems.
Scalable Development
Creating production-ready applications with maintainable code, performance-focused design, and clear system structure.
Backend Architecture
Designing APIs, data flows, and infrastructure that stay stable as traffic and feature complexity grow.
Full Stack Developer
Freelance & Open Source
Building production web apps with Next.js, Flask, and PostgreSQL for businesses and independent clients.
B.Tech in Information Technology
Amity University, Noida
Studying software engineering, data systems, cloud fundamentals, and modern product development practices.
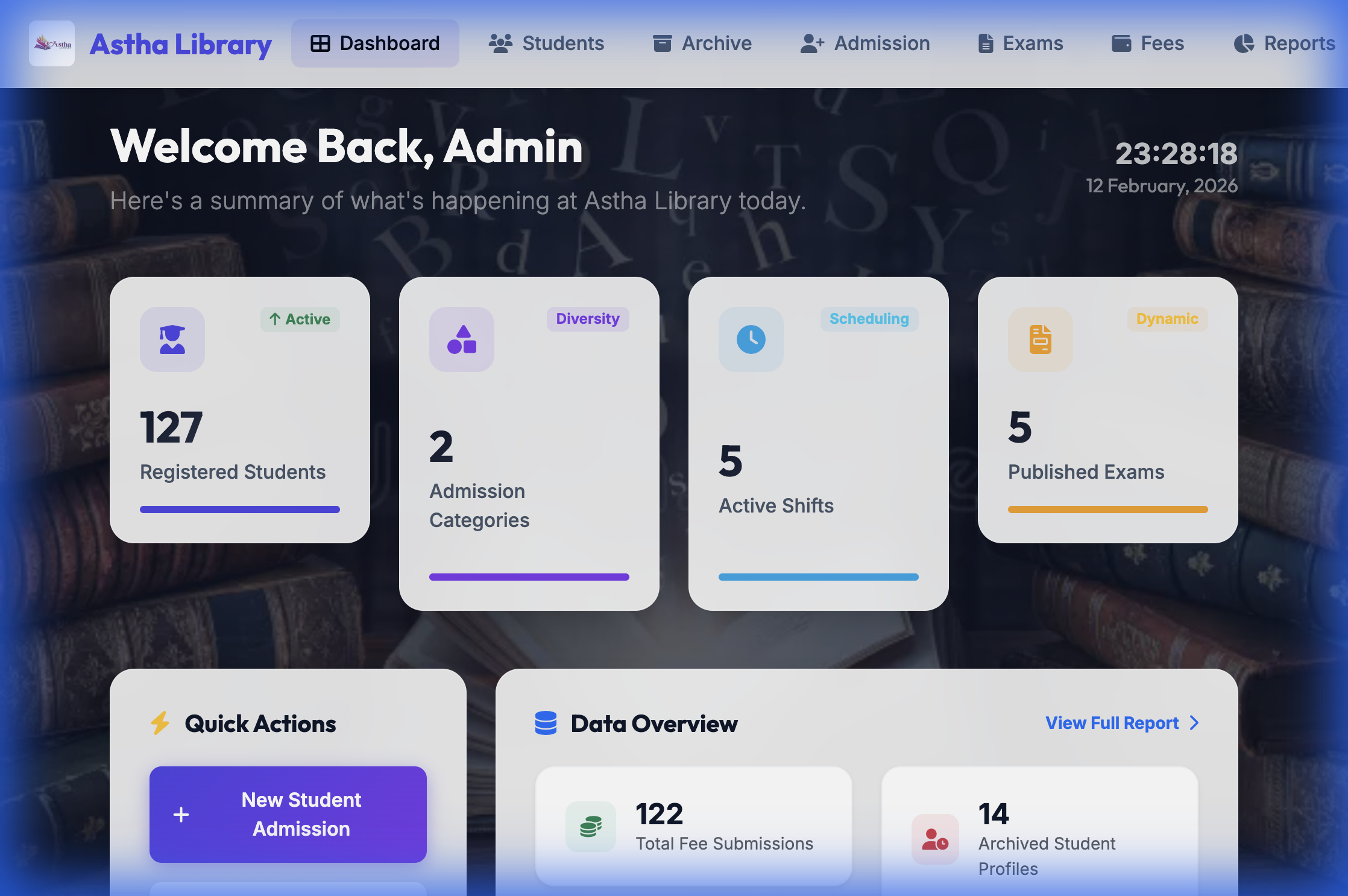
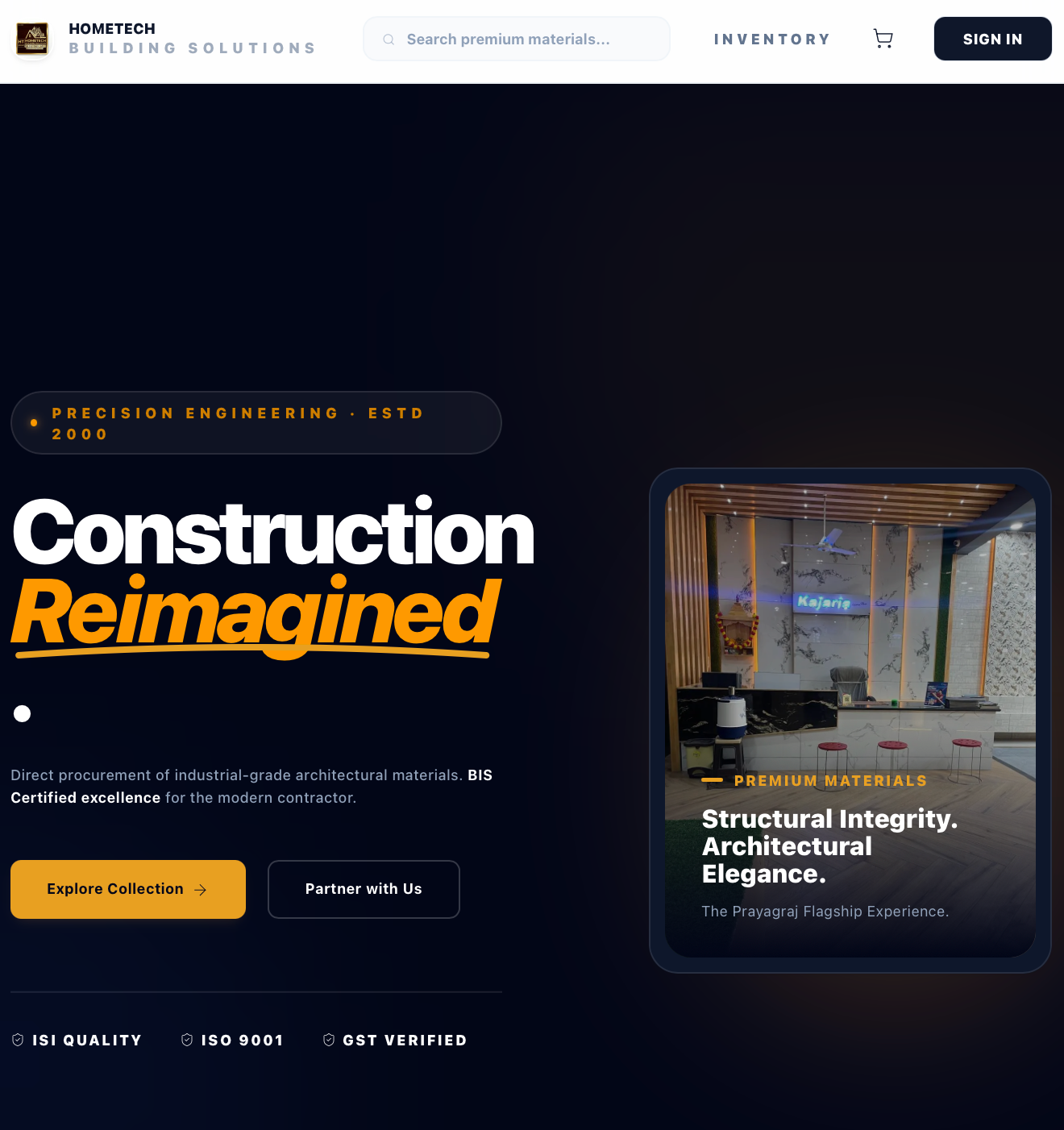
FEATURED PROJECTS
Production-grade digital products
TECH STACK
Tools I build with
React & Next.js
Building production-grade web applications with strong UX, reliable architecture, and clean code standards.
Python
Node.js
Express.js
PostgreSQL
Flask
REST API Design
Linux
Tailwind CSS
Git / GitHub
WHAT I BUILD
Full Stack Development
Building complete web applications from polished interfaces to dependable backend services.
Backend Engineering
Designing scalable APIs and server workflows that support real product growth.
Data & API Architecture
Structuring data models and integrations for clarity, performance, and maintainability.
UI Engineering
Translating design ideas into responsive, high-quality user experiences with modern frontend tooling.
Workflow Optimization
Improving development flow with clean Git practices, reusable patterns, and better team velocity.
Full Stack Architecture
End-to-end system planning from database design to deployment and iteration.